Security Fix for Path Traversal - huntr.dev #2
Add this suggestion to a batch that can be applied as a single commit.
This suggestion is invalid because no changes were made to the code.
Suggestions cannot be applied while the pull request is closed.
Suggestions cannot be applied while viewing a subset of changes.
Only one suggestion per line can be applied in a batch.
Add this suggestion to a batch that can be applied as a single commit.
Applying suggestions on deleted lines is not supported.
You must change the existing code in this line in order to create a valid suggestion.
Outdated suggestions cannot be applied.
This suggestion has been applied or marked resolved.
Suggestions cannot be applied from pending reviews.
Suggestions cannot be applied on multi-line comments.
Suggestions cannot be applied while the pull request is queued to merge.
Suggestion cannot be applied right now. Please check back later.
https://huntr.dev/users/alromh87 has fixed the Path Traversal vulnerability 🔨. alromh87 has been awarded $25 for fixing the vulnerability through the huntr bug bounty program 💵. Think you could fix a vulnerability like this?
Get involved at https://huntr.dev/
Q | A
Version Affected | ALL
Bug Fix | YES
Original Pull Request | 418sec#1
Vulnerability README | https://github.com/418sec/huntr/blob/master/bounties/npm/marscode/1/README.md
User Comments:
📊 Metadata *
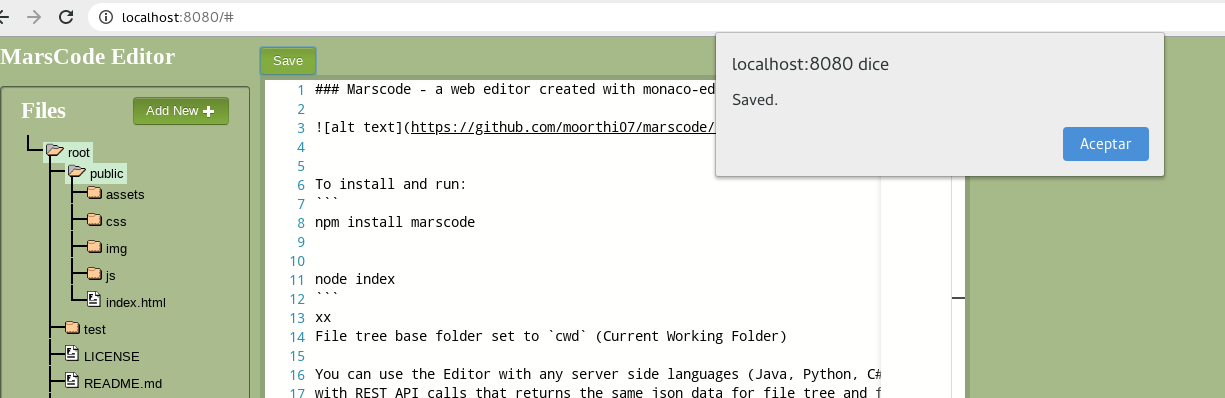
marscode is a web editor created with monaco-editor, jquery file tree and nodejs file tree to read, write, edit, delete (CRUD) files.
Affected versions of this package are vulnerable to Directory Traversal.
Bounty URL: https://www.huntr.dev/bounties/1-npm-marscode/
⚙️ Description *
There is no path sanitization in the path provided making marscode vulnerable against path traversal through the ../ technique, leading to information exposure and file content disclosure.
💻 Technical Description *
Fixed by sanitizing any occurrence of ../, using regexp.
🐛 Proof of Concept (PoC) *
node index.jscurl -v --path-as-is http://127.0.0.1:8080/../../../../../../../../../../../etc/passwd🔥 Proof of Fix (PoF) *
After fix Response code 400 Bad request is returned to user instead of restricted file content

👍 User Acceptance Testing (UAT)
After fix functionality is unafected