-
Notifications
You must be signed in to change notification settings - Fork 3
Generate Nt* system call sequence #1
Description
I have managed to run the code after which we have some doubts. Please clear some of those. The primary motive is to get a list of sequence Nt* calls as you have used in your paper System Call-Based Detection of Malicious Processes.
-
The database generated contains only the processes and their path such as chrome.exe etc. How should we extract the 'Nt*' process calls from the same?

-
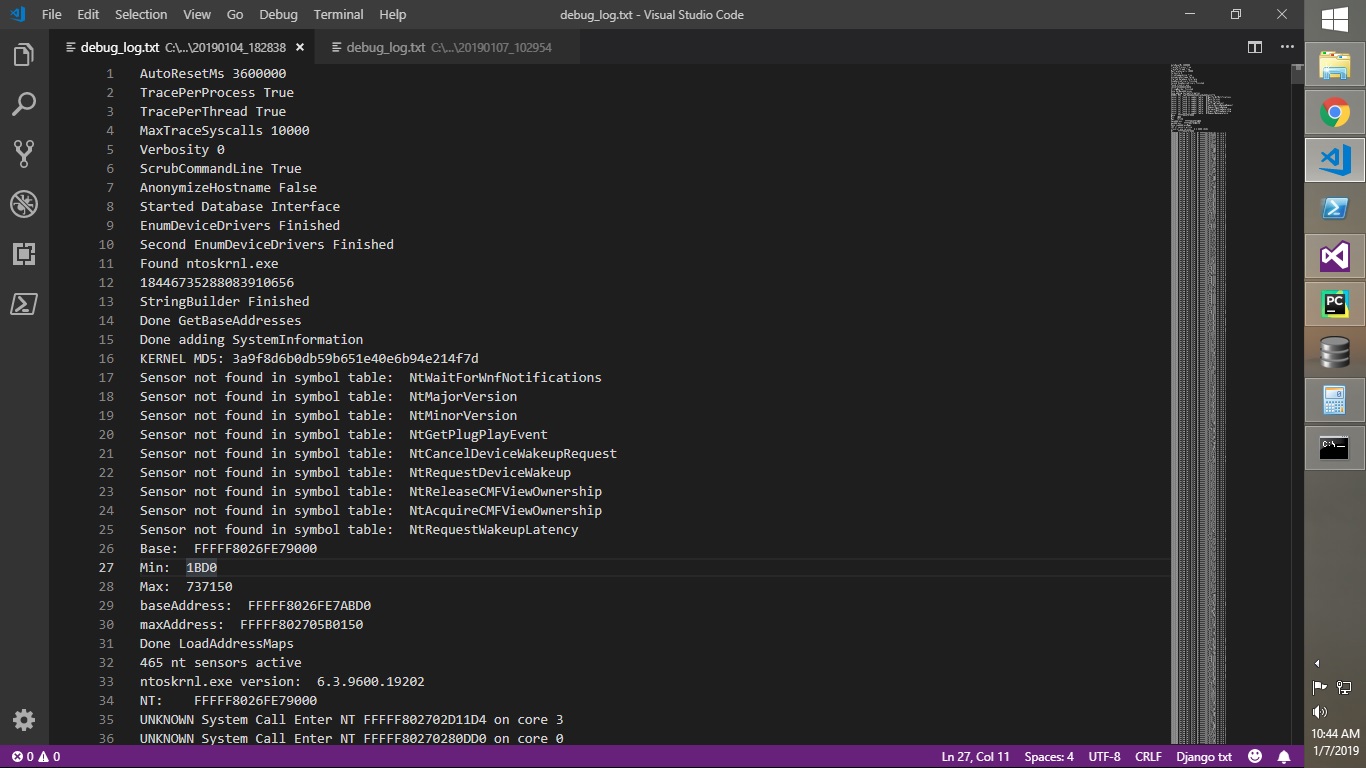
debug_log.txt contains too many lines mentioning something like this but with different addresses 'UNKNOWN System Call Enter NT FFFFF802702D11D4 on core 3. ' What is this address pointing?
EDIT:
-
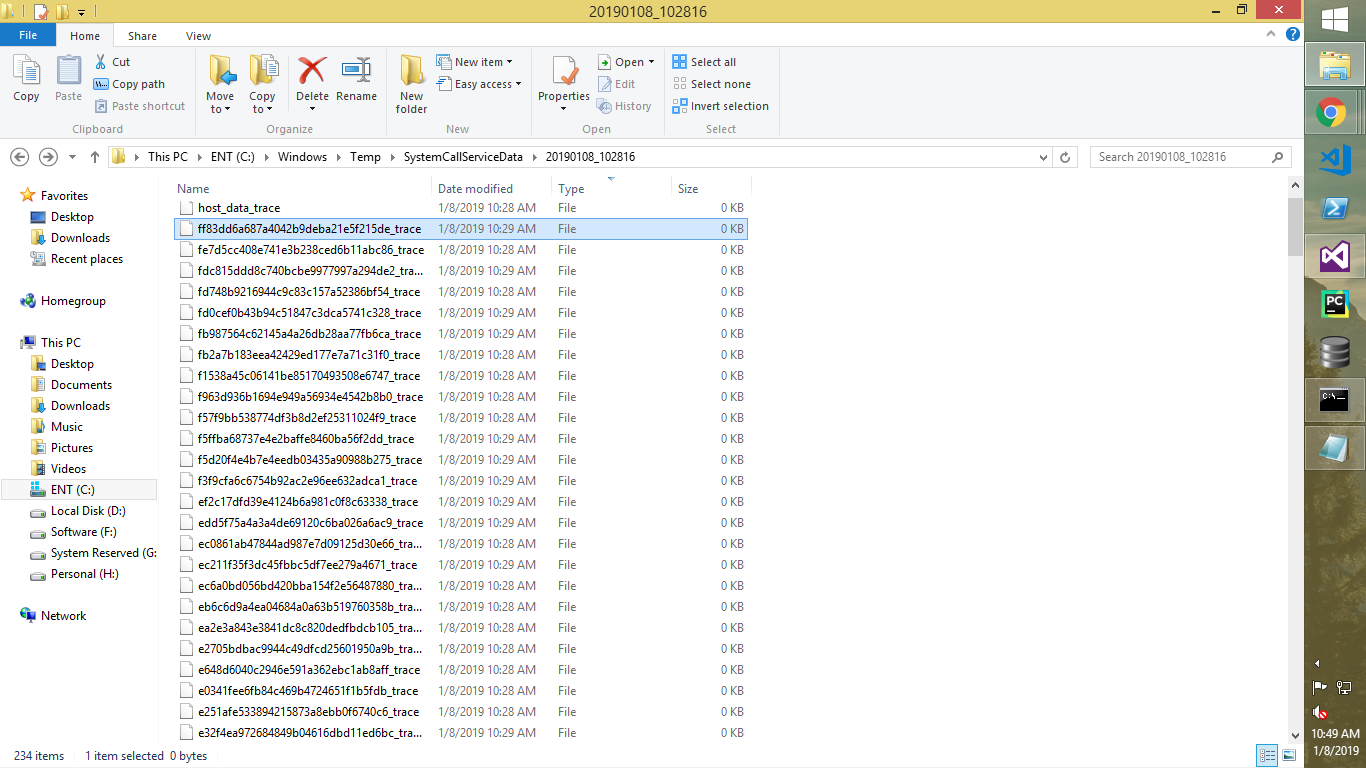
In one of our Windows 7 systems, we have got
*_tracefile with some size. Since they are binary files written usingBinaryWriter, how should I open it and read it's content? (Same is the case withhost_trace_data -
When executing the tool in the util directory, it is generating an empty symbol file.